HID stories - Page 58
HID is a key player in the physical access control and trusted identity solutions space, focusing on innovations that enhance security, efficiency, and user experience across various sectors. Their work encompasses mobile access technologies, biometric authentication, cloud-based credential issuance, and integration of AI to advance security protocols.
Through their reports and product launches, HID highlights critical trends such as mobile IDs, AI-driven access management, sustainability in security systems, and the shift towards digital and AI-powered credentialing. By exploring HID-related stories, readers can gain insights into the evolving landscape of access control technologies, risk management in cyber and physical security, and the growing emphasis on seamless, secure user authentication methods.
Whether you’re interested in the impact of emerging technologies like AI and biometrics on identity verification or the strategic adoption of cloud solutions to streamline security operations, the content tagged with HID offers valuable knowledge for IT professionals, security managers, and technology enthusiasts looking to stay informed about advancements and challenges in trusted identity and access control.
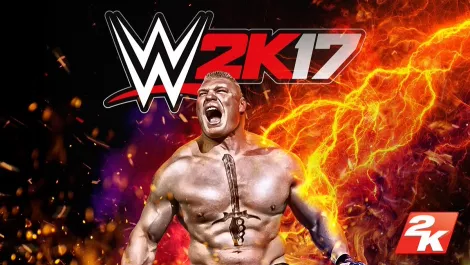
Review: WWE 2K17 is still lingering in the midcard

Ransomware: Expert advice on how to keep safe and secure

Hands-on Review: Lenovo's ThinkPad X1 Tablet
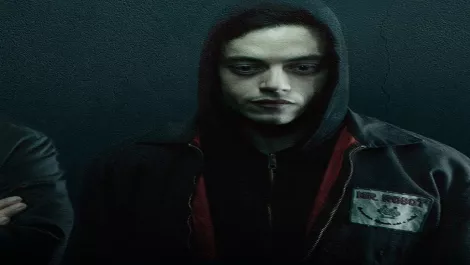
10 cybersecurity lessons learned from Season 2 of Mr. Robot

The incredible system that every IT department needs

'Modern cities' may be smarter, but they're not much safer
Polycom's Jeff Rodman on partnerships, innovation, collaboration & creativity

Selling enterprise security solutions - tips for success

Hands-on Review: Sony MDR1000x Bluetooth Headphones

Trend Micro tackles ransomware threat with new software

PHOTO GALLERY: The all new iPhone and Series 2 Apple Watch

Xbox Fanfest event is beaming down to Sydney, Australia

Hands-on Review: Parallels Desktop 12 for Mac

Fighting a hidden enemy: Singapore cybersecurity in this hyper-connected era

Measuring the high costs of web malware protection

Hands-on Review: Lenovo MiiX 700 Tablet - the best of all worlds

Intel Skull Canyon NUC: When size doesn't matter

The unbalanced fight against network security threats

ESET discovers new Android botnet controlled by Twitter
