The Ultimate Guide to Email Security
A curated Asian edition of TechDay news, analysis, interviews, reviews, job moves, and related resources for Email Security.
What to know about Email Security
Email Security is a vital domain focused on protecting email communication from a myriad of cyber threats that target individuals and organizations alike. With email being a primary vector for delivering malware, launching phishing campaigns, and executing business email compromise (BEC) scams, robust email security measures are essential to safeguard sensitive information and maintain trust in digital correspondence.
Recent developments reveal a surge in sophisticated email attacks leveraging artificial intelligence to craft convincing phishing attempts and evade traditional defenses. Innovations in AI-powered threat detection, incident response automation, and advanced authentication protocols are shaping the future of email security, providing organizations with enhanced capabilities to detect and mitigate evolving threats.
Exploring stories on Email Security allows readers to stay informed about emerging tactics used by cybercriminals, new security solutions introduced by industry players, and best practices to fortify their email systems. Understanding these trends helps businesses and individuals recognize vulnerabilities, respond effectively to incidents, and build resilient email communication infrastructures in an increasingly digital and threat-prone landscape.
Asian Email Security News
Regional stories with direct local relevance
Canon Singapore launches cybersecurity suite with ESET
Businesses facing rising phishing attacks in Singapore now have access to Canon's new suite, which covers monitoring, training and incident response.

KnowBe4 expands Asia push amid rising email threats
Rising email fraud is driving KnowBe4's regional expansion, as security chiefs warn that AI-made attacks are targeting Asia's businesses.

Singapore phishing drill cuts clicks as training pays
Repeated phishing training helped cut Singapore staff click rates to 7.4% from 17%, despite more than 8,500 fake emails sent.

Singapore firms face AI security incidents despite controls
Half of Singapore organisations with AI security coverage still reported a confirmed or suspected incident, exposing gaps in monitoring and response.

SEON eyes doubling Indonesia revenue as fraud risk rises
Rising scam losses and tighter oversight are fuelling demand for SEON’s fraud tools, with Indonesia set to be a key growth market.

Japan urged to speed 5G rollout & boost digital trust
Stronger safeguards and faster rollout could help Japan turn advanced connectivity into wider economic gains as scams and exclusion persist.
Analyst Insights
Research and market analysis connected to Email Security
Group-IB named a Leader in Gartner cyberthreat report

Check Point tops Miercom hybrid mesh security benchmark

iProov report warns of soaring iOS injection attacks

Survey finds organisations struggle to secure unstructured data

DigiCert posts record ARR after Valimail acquisition
Featured News
Expert Columns

Your Immune System Doesn't Wait. Neither Should Your Security

Why service desks are emerging as a critical security weakness

Stolen credentials don't have to mean a breach

One click can trigger a breach, but security can stop it
Building security outcomes for small businesses: Why breaches persist despite available tools

Agentic AI: The potential and the problems behind the new wave of autonomous systems

Hexnode CEO on how fintech breaches multiply where device visibility ends

Saving the weekend: How SonicWall's SonicSentry SOC stopped a Saturday night cyberattack

Kernel in the crosshairs: The BlackSanta threat campaign targeting recruitment workflows

A resilient security culture is built in the flow of work, not the classroom
Interviews
Interviews and video coverage from the networkRecent Email Security News

Check Point & MyRepublic launch SME email security
Singapore SMEs can now buy managed email protection as phishing attacks rose 49% in 2024, with AI-generated lures increasingly involved.

Microsoft 365 behind 32% of escalated security incidents
Cloud office accounts are emerging as a major weakness in Malaysia, with 3,945 confirmed incidents tied to Microsoft 365 in 2025.

Singaporeans want phone support as firms push digital
Singaporeans still prefer calls for customer support, but firms are shifting budgets to digital self-service and AI, risking a widening gap.
Vietnam fake account farms fuel global cybercrime wave
Vietnam-based fake account farms are fuelling a growing global cybercrime market, flogging cheap logins, bot tools and disposable email tricks.

Delta unveils zero-deductible cyber cover in Singapore
Delta launches zero-deductible cyber cover in Singapore, promising instant quotes via a five-point digital assessment for SMEs across Asia.

Indonesia launches SHECURE Digital to protect women online
Indonesia has launched SHECURE Digital, a national programme to shield women and girls from online abuse, extortion and data exploitation.

Phishing & smishing scams surge across Philippines
Phishing and smishing scams in the Philippines surged in 2025, with phishing sites jumping 423% as fraud shifts to mobile and social media.

CelcomDigi survey to tackle AI-driven scams at unis
CelcomDigi launches nationwide survey to learn how Malaysian uni students spot AI-driven scams and shape stronger online safety tools.

Indosat's AI spam shield blocks scams worth USD $500m
Indosat's AI spam shield blocked 2bn risky contacts in six months, averting scam losses of about USD $500m for Indonesian users.

CelcomDigi & Firebase launch telco-based verification
CelcomDigi, Firebase and Telenor Linx launch network-based phone verification in Malaysia to replace vulnerable SMS one-time passwords.

AI-driven cyber attacks surge in Check Point 2026 report
AI-fuelled cyber attacks surged 70% in 2025, with Check Point warning of machine-speed, multi-channel campaigns targeting key sectors.
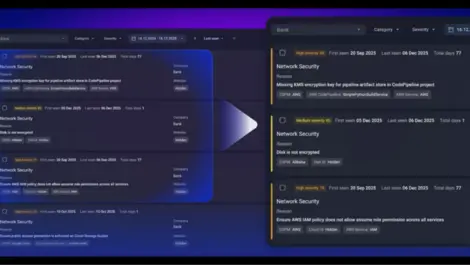
Group-IB adds CSPM to Unified Risk Platform for cloud
Group-IB has added cloud security posture management to its Unified Risk Platform, automating misconfiguration detection and compliance checks.

Indonesia launches national cyber resilience drive
Indonesia launches a six-month cyber resilience drive to train over 1,000 leaders and practitioners in practical defence and governance.

Coupang breach & camera hacks expose Asia cyber gaps
A vast Coupang data breach and mass camera hacks in South Korea expose Asia's widening cyber security gaps and weak identity defences.

Why cyber resilience is now a CFO priority
Hong Kong CFOs now prioritise cyber resilience as cyberattacks increasingly risk financial stability, compliance and corporate reputation across sectors.

CelcomDigi reaches 4 million with anti-scam campaign on TV & online
CelcomDigi and Media Prima's anti-scam campaign has reached over 4 million Malaysians, raising awareness of online scams via TV and digital platforms.
Google & CSA join forces to boost Singapore cyber resilience
Google and Singapore's Cyber Security Agency renew partnership to enhance national cybersecurity with AI tools and public-private training initiatives.

Synology launches DSM 7.3 with advanced AI & security tools
Synology launches DSM 7.3, enhancing storage efficiency, security, collaboration, and AI-driven data protection for modern enterprises.

Lazarus subgroup deploys trio of RATs in finance sector attacks
Lazarus subgroup deploys three remote access trojans, including PondRAT and ThemeForestRAT, to target financial and cryptocurrency organisations with advanced cyberattacks.

Singapore firms lead in AI security but face shadow AI threat
Singaporean firms lead globally in AI security readiness but face the highest incidence of risky unsanctioned shadow AI use, raising significant governance concerns.



